OpenAI confirms compromise in TanStack npm supply chain attack
OpenAI confirmed compromise in the TanStack npm supply chain attack by TeamPCP. Two employee devices were infected through malicious packages, giving attackers access to limited internal repositories and credential material. No customer data, production systems, or deployed software were affected. Incident response blocked insertion of malicious code. The company is rotating code-signing certificates and adding controls. TeamPCP is linked to the Mini Shai-Hulud campaign.
⚠️ PSA: If you are un-aware of the latest supply-chain attacks, or aware but complacent and didn't do anything, especially if you're running Hermes/OpenClaw or manage them for other folks, read this, it'll take 3 minutes i promise.
Supply Chain poisoning attacks are especially vicious, they often compromise a package (javascript packages via NPM, python via PyPI) that is not installed directly, but is a requirement from something else you install.
So if your agent is building software for ya, or is downloading skills, or even is updating itself, your mac can get infected by this rotten supply chain.
These are not viruses, rather, malware worms, and since many are running agents without a sandbox, with code writing and execution permissions and give their agents full credentials to their email, personal life, API keys etc, these attackers harvest every possible personal data under the sun, API keys in .env, browser sessions, crypto keys, you name it.
There are generally 2 ways of "protecting" your agent (and yourself) from something like this.
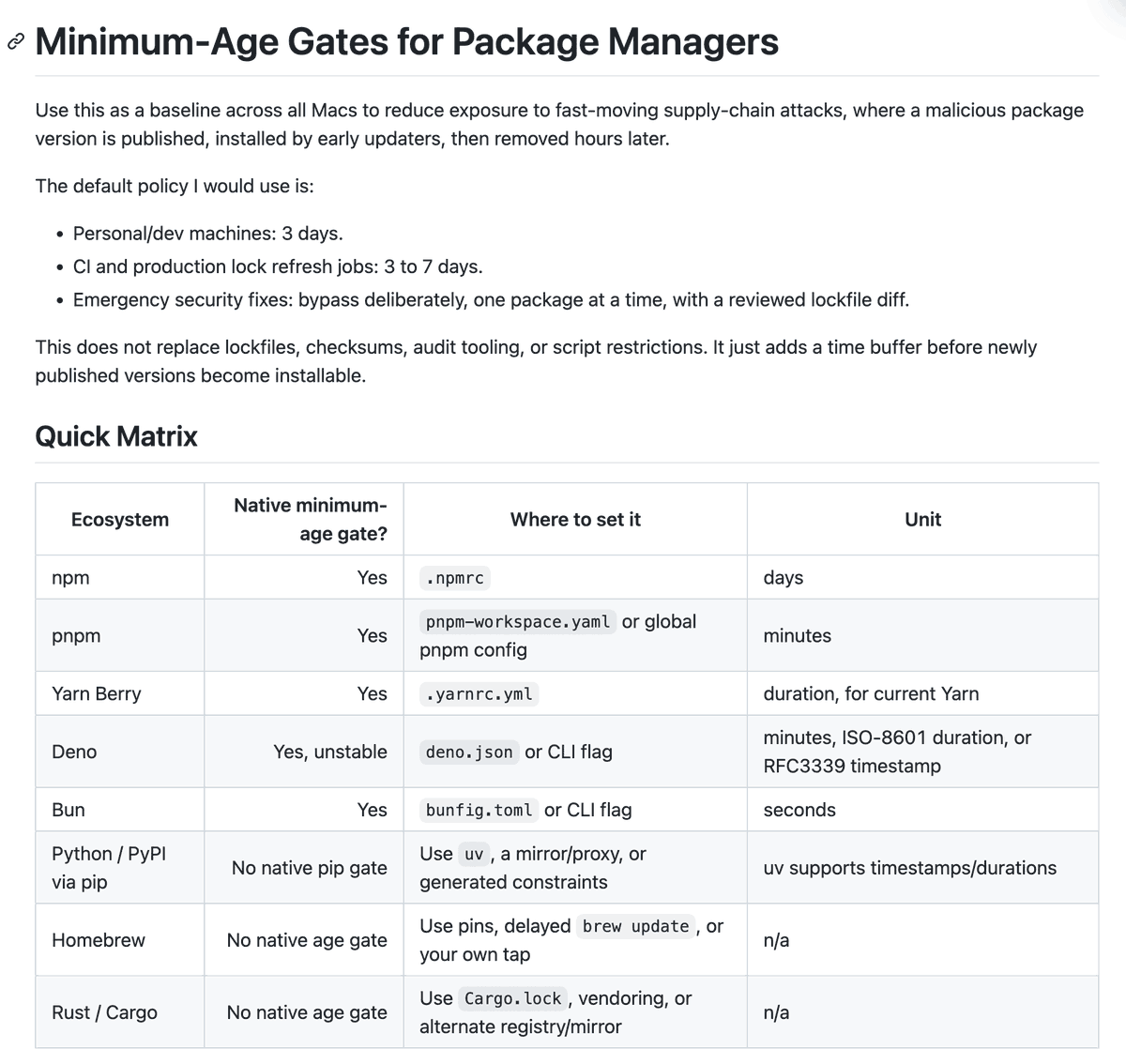
1) Sandboxed execution - Run your Hermes/OpenClaw on a dedicated sandbox, Docker or otherwise. 2) Restrict minimum-age of package installation
Number 2 is the most important, it assumes that package managers will detect an attack within 24-ish hours and will take down the infected packages from the registries. So if you want to be security conscious, you need to set global rules for your package managers to never install a new update that's less than 24 hours old.
Here's a guide Codex helped me publish that shows your agent how to set these rules up on your machines: https://gist.github.com/altryne/233ea8c8446c1ed0aead7561aeeca213
For this latest Mini-Shai Hulud worm, it's vicious specifically because it self replicates, and removing the packages doesn't remove the worm.
@nisten has written a scanner that you can ask your agent to run to see if you were compromised.
Additionally, we covered this on @thursdai_pod - it's good practice to always create dedicated API keys for each specific agent/machine and clearly designate them. Storing them in a password manager like @1Password and @Bitwarden helps with tracking and rolling if you were exposed.
Don't be complacent, this new wave of supply chain attacks seems to be fueled by more powerful AI coding agents, and it'll take time to stabilize, in the meanwhile, stay protected.
Meanwhile the big labs continue to push for gating models while the open source ecosystem they (and everyone else rely on) and the small closed source software companies go unprotected.
You can't fix 100 buildings in a city of 2 million buildings and think the job is done.
Wide distribution is the only defense. AI defense beats AI attack.
‼️🚨 This is wild. OpenAI just confirmed it got hit in the TanStack npm supply chain attack, and the attackers were close to being able to ship malicious code inside official OpenAI software, signed and trusted, if their incident response had not caught it in time. The campaign is the work of TeamPCP, the same crew running the Mini Shai-Hulud wave. Two employee devices in OpenAI's corporate environment were compromised through the malicious TanStack packages. The attackers used that foothold to reach a limited subset of internal source code repositories. OpenAI says only "limited credential material" was successfully exfiltrated, with no customer data, production systems, intellectual property or deployed software impacted. Here is the part that should grab your attention. OpenAI is rotating its code-signing certificates and forcing every macOS user to update their OpenAI apps. You do not rotate signing certs for "limited credential material." You rotate signing certs when the attacker was close enough to signing malicious binaries as OpenAI. The "we contained it in time" framing is doing serious heavy lifting here. For wider context, the same TeamPCP wave also hit Mistral AI, UiPath, Guardrails AI, OpenSearch and SAP npm packages. The TanStack compromise is tracked as CVE-2026-45321 at CVSS 9.6, and Mistral AI source code is already being advertised for sale by the group.
Meanwhile the big labs continue to push for gating models while the open source ecosystem they (and everyone else rely on) goes unprotected.
You can't fix 100 buildings in a city of 1 million buildings and think the job is done.
Wide distribution is the only defense. AI defense beats AI attack.
‼️🚨 This is wild. OpenAI just confirmed it got hit in the TanStack npm supply chain attack, and the attackers were close to being able to ship malicious code inside official OpenAI software, signed and trusted, if their incident response had not caught it in time. The campaign is the work of TeamPCP, the same crew running the Mini Shai-Hulud wave. Two employee devices in OpenAI's corporate environment were compromised through the malicious TanStack packages. The attackers used that foothold to reach a limited subset of internal source code repositories. OpenAI says only "limited credential material" was successfully exfiltrated, with no customer data, production systems, intellectual property or deployed software impacted. Here is the part that should grab your attention. OpenAI is rotating its code-signing certificates and forcing every macOS user to update their OpenAI apps. You do not rotate signing certs for "limited credential material." You rotate signing certs when the attacker was close enough to signing malicious binaries as OpenAI. The "we contained it in time" framing is doing serious heavy lifting here. For wider context, the same TeamPCP wave also hit Mistral AI, UiPath, Guardrails AI, OpenSearch and SAP npm packages. The TanStack compromise is tracked as CVE-2026-45321 at CVSS 9.6, and Mistral AI source code is already being advertised for sale by the group.